Gabriela Marcos
PTaaS (PenTesting as a Service) is an innovative cloud-based solution that empowers organizations to effortlessly perform comprehensive cybersecurity tests on their applications, systems and networks. Gartner has recognized PTaaS as an emerging technology in its Security Operations hype-cycle, positioning it to supplant traditional PenTesting.
Check out this short article to discover the amazing reasons why it's being adopted by organizations all around the world!
Why Use PTaaS?
PTaaS (Penetration Testing as a Service) platforms offer numerous advantages compared to traditional pen testing methods. With real-time, continuous security testing, PTaaS provides organizations with a cutting-edge approach to enhancing their security posture.
Here are some key benefits of PTaaS:
- Timely detection and management of vulnerabilities, ensuring proactive security measures
- Continuous assessments, eliminating the limitations of periodic pen testing
- Actionable insights and recommendations, empowering security teams to make informed decisions
- Enhanced agility and flexibility in adapting to evolving threats and technology landscapes
- Cost-effective solution, reducing the need for in-house resources and infrastructure
- Scalability and on-demand testing, accommodating the needs of organizations of all sizes
- Streamlined reporting and documentation, facilitating clear communication and compliance efforts
- By leveraging PTaaS, organizations can stay one step ahead in the ever-changing cybersecurity landscape, bolstering their defenses and safeguarding critical assets.
Comparison to Traditional PenTesting
When it comes to comparing PTaaS (Penetration Testing as a Service) with traditional pen testing, there are several key differences to consider:
Cost-effectiveness: PTaaS offers a more budget-friendly solution compared to traditional penetration testing. With PTaaS operating on a Software as a Service (SaaS) model, businesses can avoid hefty upfront costs and instead pay for the services they need as they go.Scalability: PTaaS provides a scalable option for businesses of all sizes. As a service-based model, PTaaS allows organizations to easily adjust their testing needs based on their requirements, without the need for additional investments in infrastructure or resources.
Time commitment: Traditional pen testing often requires a significant time commitment, with lengthy processes and manual efforts. In contrast, PTaaS streamlines the testing and reporting process, leveraging automation and specialized tools to deliver faster results and reduce the overall testing timeline.
Continuous Compliance: PTaaS ensures that you always have a fresh report that can be generated on-demand, giving you the latest picture of your security posture. This is a big when compared to traditional PenTesting reports that can be months (or even years) old.
By embracing PTaaS, businesses can benefit from its cost-effectiveness, scalability, and time-saving advantages, making it an attractive choice for ensuring robust security measures.
Is it Automated PenTesting?
PTaaS (Penetration Testing as a Service) is more than just automated pen testing. It offers a comprehensive approach to cybersecurity testing that combines the power of automated testing tools with the expertise of manual testing techniques performed by skilled PenTesters. This unique combination ensures a thorough and robust testing program, covering all critical areas that automated tools alone might miss.
Here are some key points to highlight:
- PTaaS incorporates multiple automated testing tools for efficient and accurate vulnerability detection (Attack Surface Mapping, Reconnaissance, Vulnerability Scanning)
- Skilled PenTesters perform manual testing techniques to identify complex vulnerabilities and eliminate false positives that require human expertise.
- The combination of automated and manual testing provides a holistic approach to security testing.
- PTaaS ensures comprehensive coverage mapping and following the evolving scope of your landscape, giving organizations confidence in the effectiveness of their security measures.
By leveraging both automated and manual testing, PTaaS delivers a high-quality testing program that goes beyond the limitations of automated tools alone.
How Does PTaaS Work?
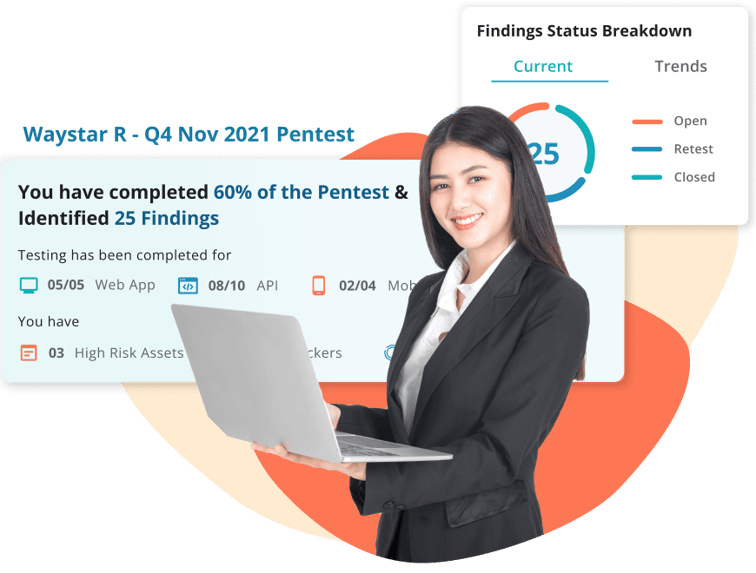
The PTaaS (Penetration Testing as a Service) delivery model seamlessly integrates with your current systems, empowering you to identify, validate, prioritize and remediate your findings seamlessly. Once your scope has been determined, you can schedule assessments through the click of button at the desired frequency you want.
By continuously testing for vulnerabilities, PTaaS identifies potential security gaps and delivers actionable insights through a robust cloud-based platform. The integrated vulnerability management module in PTaaS allows you to track a finding from identification to remediation. Detailed steps to reproduce and proof of concepts are also delivered via the platform which makes a developers life easy.
Integrations with workflow and productivity tools also ensure that findings can be tracked using your existing tool stack. In built collaboration tools allow your developers to interact with PenTesters who logged the findings to obtain more clarity.
Finally, the automated reporting features of PTaaS enables you to generate 'One Click' reports that will satisfy a variety of external and internal compliance requirements (like SOC2, ISO, PCI) and customer mandates.
In short PTaaS platforms enables the following:
Continuous testing: PTaaS provides ongoing vulnerability assessment, ensuring your systems are protected against evolving threats.Real-time reporting: Stay informed with instant reports on identified vulnerabilities, allowing your security team to take immediate action on test results.
Actionable insights: PTaaS goes beyond just identifying vulnerabilities; it provides practical recommendations to address security gaps effectively.
Integrated approach: Rather than occurring in a silo like traditional PenTests, PTaaS integrates with your existing tool stack and workflows to accelerate vulnerability remediation.
In built collaboration: You always have access to expert PenTesters, making it easy to reproduce an issue or identify a compensating control.
'One click' automated reports: Reporting is often the most mundane and time consuming activity of PenTesting. PTaaS completely does away with this and makes reporting one of your easiest tasks to do.
Key takeaways
PTaaS offers organizations a comprehensive and continuous offensive security and vulnerability management solution, facilitating compliance enablement. With real-time reporting and actionable insights, your security team is empowered to promptly address vulnerabilities, ensuring your overall security posture meets regulatory requirements.
With PTaaS, you can strengthen your security program, mitigate risks, and safeguard your business against potential security threats. It's all about fortifying your defenses and staying one step ahead of the game!